How they can hack your mobile
The cell phone has become such an important and extremely careful personal item that if a stranger...

The cell phone has become such an important and extremely careful personal item that if a stranger...

Cyber scams are common among unsuspecting users, but sometimes strategies to steal data or money go beyond...

Email scams are the order of the day. The worst of all is that they are increasingly...

May WhatsApp be the most downloaded and used instant messaging application in the world, backed by its more than 600...

Nowadays there are many ways to capture or intercept someone's information. In our post we will talk to you about...
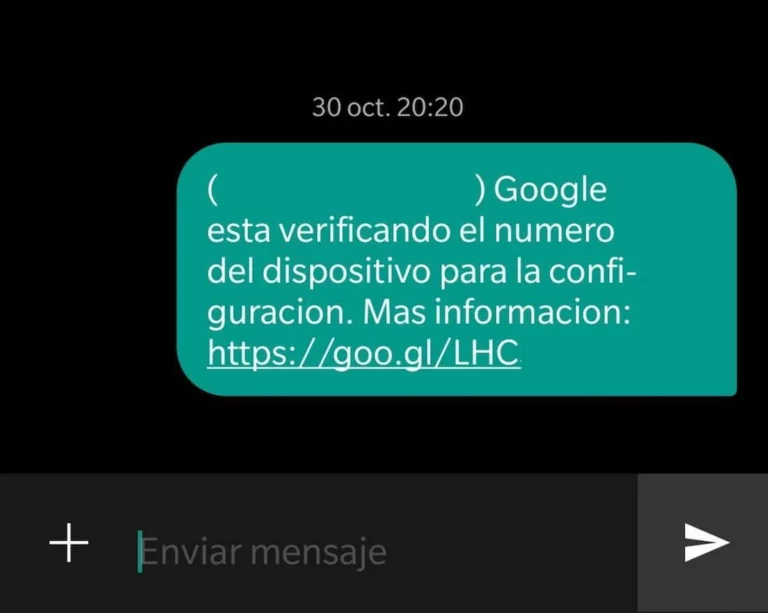
Traditional text messages, or SMS, have lost presence compared to instant messaging. However, even today...

Browsing the Internet exposes us, if we do not take measures, to advertising and surprising links that appear in different parts of...
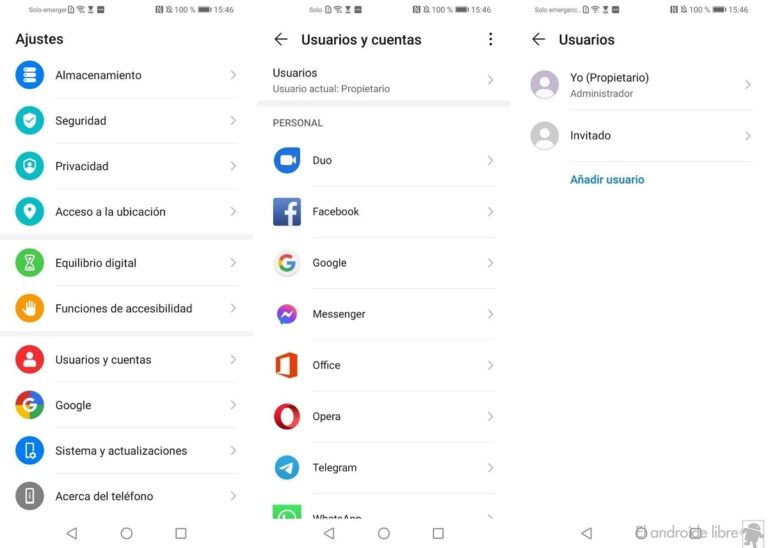
Hiding applications is a procedure that we can carry out on Android so that other people do not easily see which apps...

You've probably heard of VPNs. This technology allows us to change our IP address and at the same time reinforce...

It doesn't happen often, but it has probably happened to you at some point in your life. This usually...
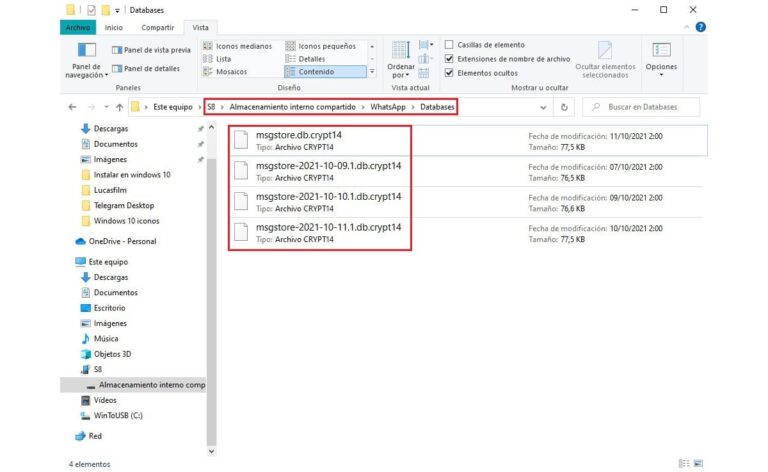
If you have ever wondered what msgstore is and what it is for, in this article we are going to solve all of them...